OpenClaw is the fastest growing agent harness out there, which can work 24/7 to automate almost any kind of tasks. However, its capabilities are limited to the tools it has access to. Composio allows your OpenClaw to access Mem0 with authentication management handled for you. You can execute actions on Mem0 via your favorite OpenClaw interface (Telegram, WhatsApp, TUI, etc), whichever you prefer.
Table of Contents
Connect Mem0 without Auth hassles
We manage OAuth, API Key, token refresh, and scopes, you just build.
Try for FreeIntroduction
Also integrate Mem0 with
Why use Composio?
Apart from a managed and hosted MCP server, you will get:
- Programmatic tool calling allows LLMs to write its code in a remote workbench to handle complex tool chaining. Reduces to-and-fro with LLMs for frequent tool calling.
- Handling Large tool responses out of LLM context to minimize context rot.
- Dynamic just-in-time access to 20,000 tools across 1000+ other Apps for cross-app workflows. It loads the tools you need, so LLMs aren't overwhelmed by tools you don't need.
How to install Mem0 with OpenClaw
Using Composio API Key and Setup Prompt
- Go to dashboard.composio.dev
- Copy the setup prompt
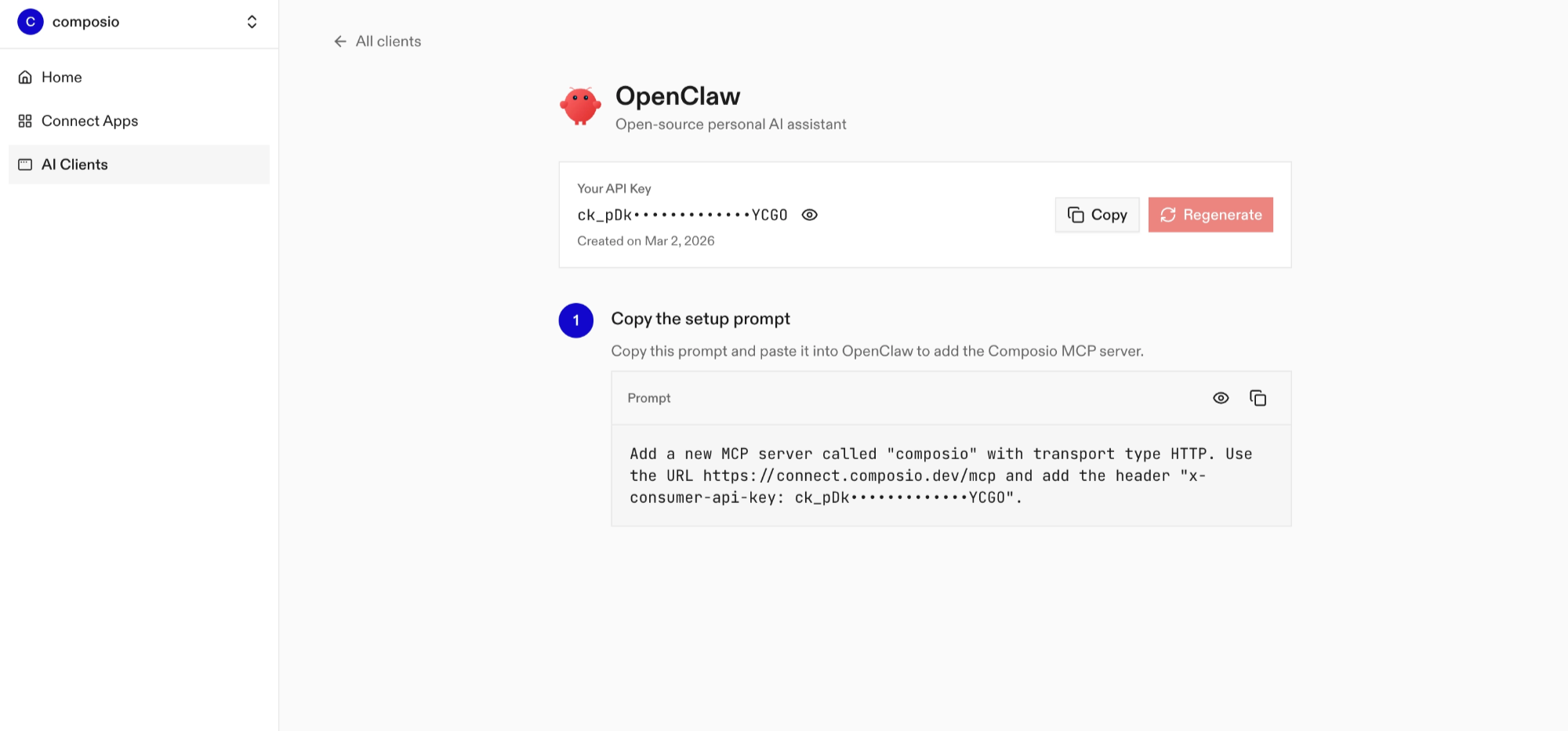
- Run it in your OpenClaw chat interface.
- Authenticate Mem0 from the dashboard
- Go back to your OpenClaw interface and start asking questions.
Using OpenClaw/Composio Plugin
1. Install OpenClaw Composio plugin
2. Copy the API Key from dashboard.composio.dev
3. Setup OpenClaw Config
4. Restart OpenClaw
5. Go to your chat interface and start asking questions.
6. When prompted, authenticate the app and you're all set.
How It Works
The plugin connects to Composio's MCP server at https://connect.composio.dev/mcp and registers all available tools directly into the OpenClaw agent. Tools are called by name — no extra search or execute steps needed.
If a tool returns an auth error, the agent will prompt you to connect that toolkit at dashboard.composio.dev.
Configuration
| Option | Description | Default |
|---|---|---|
enabled | Enable or disable the plugin | true |
consumerKey | Your Composio consumer key (ck_...) | — |
mcpUrl | MCP server URL (advanced) | https://connect.composio.dev/mcp |
What is the Mem0 MCP server, and what's possible with it?
The Mem0 MCP server is an implementation of the Model Context Protocol that connects your AI agent and assistants like Claude, Cursor, etc directly to your Mem0 account. It provides structured and secure access to your notes, projects, and organizational knowledge, so your agent can perform actions like searching memories, managing users, adding content, and orchestrating agent runs on your behalf.
- AI-powered memory search and recall: Let your agent search and retrieve existing memory entries using advanced filters and pagination to surface just the right note or piece of information.
- Automated content and note creation: Have your agent store new memory records from conversations, meetings, or tasks—ensuring nothing slips through the cracks.
- Collaboration and organization management: Direct your agent to add members to projects or organizations, assign roles, and keep team structures up to date.
- Agent and application orchestration: Enable your agent to create new AI agents, initiate agent runs, and manage applications for custom workflows and automation.
- Structured knowledge export and reporting: Ask your agent to initiate export jobs with specific schemas and filters, so you can back up or analyze your stored knowledge on demand.
Supported Tools & Triggers
Conclusion
You've successfully integrated Mem0 with OpenClaw using Composio plugin. Now interact with Mem0 directly from your terminal, Web UI, or any messenger app using natural language commands.
Key benefits of this setup:
- Seamless integration across TUI, Web UIs, and Messenger apps like Telegram, WhatsApp, Slack, etc.
- Natural language commands for Mem0 operations
- Managed authentication through Composio
- Access to 20,000+ tools across 1000+ apps for cross-app workflows
- Programmatic tool calling for complex tool chaining
Next steps:
- Try asking OpenClaw to perform various Mem0 operations
- Explore cross-app workflows by connecting more toolkits like Calendar, Slack, Notion, etc.
- Build complex automation scripts that leverage OpenClaw's 24/7 running capabilities