Codex is one of the most popular coding harnesses out there. And MCP makes the experience even better. With Cloudflare MCP integration, you can draft, triage, summarise emails, and much more, all without leaving the terminal or the app, whichever you prefer.
Table of Contents
Connect Cloudflare without Auth hassles
We manage OAuth, API Key, token refresh, and scopes, you just build.
Try for FreeIntroduction
Also integrate Cloudflare with
Why use Composio?
Apart from a managed and hosted MCP server, you will get:
- CodeAct: A dedicated workbench that allows GPT to write its code to handle complex tool chaining. Reduces to-and-fro with LLMs for frequent tool calling.
- Large tool responses: Handle them to minimise context rot.
- Dynamic just-in-time access to 20,000 tools across 1000+ other Apps for cross-app workflows. It loads the tools you need, so GPTs aren't overwhelmed by tools you don't need.
How to install Cloudflare MCP in Codex
Run the setup command
Run this command in your terminal to add the Composio MCP server to Codex.
It will initiate the authentication in a browser window, authorize Codex to access your Composio account.
(Optional) Authenticate with OAuth
To authenticate manually, run the login command to open a browser window and authorize Codex to access your Composio account.
Verify the connection
Run codex mcp list to confirm Composio appears as a registered MCP server.
Codex App
Codex App follows the same approach as VS Code.
- Click ⚙️ on the bottom left → MCP Servers → + Add servers → Streamable HTTP:
- Fill the header and Key fields with
{ "x-consumer-api-key" = "ck_*******" }. - The Key is the Composio API key, that you can find on dashboard.composio.dev
- Click on Authenticate and authorize Codex to your Composio account and you're all set.
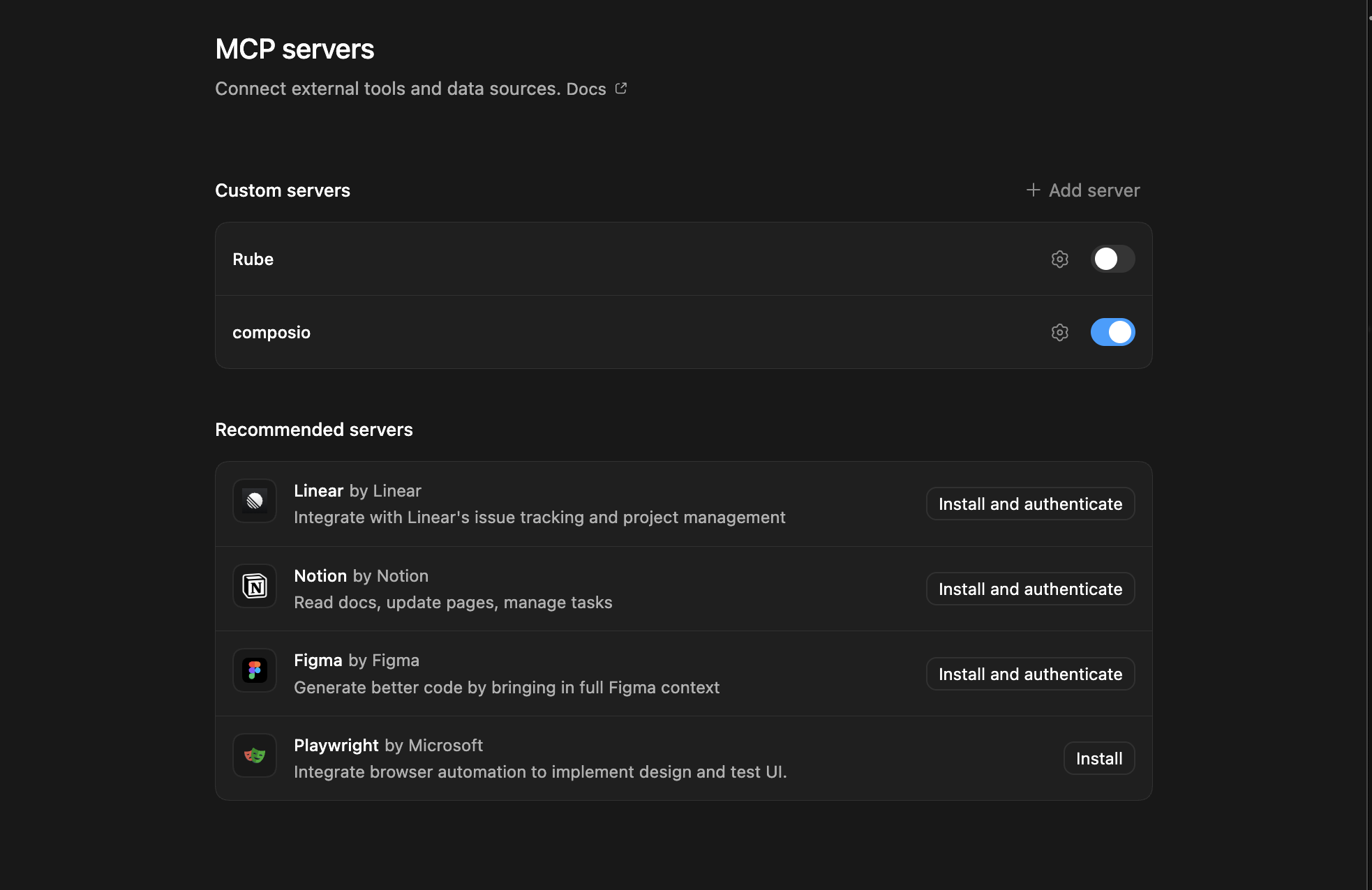
- Restart and verify if it's there in
.codex/config.toml
What is the Cloudflare MCP server, and what's possible with it?
The Cloudflare MCP server is an implementation of the Model Context Protocol that connects your AI agent and assistants like Claude, Cursor, etc directly to your Cloudflare account. It provides structured and secure access to your Cloudflare infrastructure, so your agent can perform actions like managing DNS records, configuring WAF lists, auditing firewall rules, and overseeing zones and account members—all on your behalf.
- DNS record management: Effortlessly create or delete DNS records within any zone, allowing your agent to automate domain setup and maintenance tasks.
- WAF list and firewall rule automation: Direct your agent to create, list, or delete Web Application Firewall (WAF) lists and audit firewall rules to enhance your site's security posture.
- Zone administration: Enable your agent to create new zones when adding domains or delete zones that are no longer needed, streamlining domain onboarding and cleanup.
- Account and member management: Let your agent list all Cloudflare accounts you have access to and enumerate members within each account for audit or collaboration purposes.
- Comprehensive infrastructure visibility: Ask your agent to fetch and review your entire Cloudflare account structure, making it simple to monitor resources and configurations at scale.
Supported Tools & Triggers
Conclusion
You've successfully integrated Cloudflare with Codex using Composio's MCP server. Now you can interact with Cloudflare directly from your terminal, VS Code, or the Codex App using natural language commands.
Key benefits of this setup:
- Seamless integration across CLI, VS Code, and standalone app
- Natural language commands for Cloudflare operations
- Managed authentication through Composio
- Access to 20,000+ tools across 1000+ apps for cross-app workflows
- CodeAct workbench for complex tool chaining
Next steps:
- Try asking Codex to perform various Cloudflare operations
- Explore cross-app workflows by connecting more toolkits
- Build automation scripts that leverage Codex's AI capabilities