Codex is one of the most popular coding harnesses out there. And MCP makes the experience even better. With Taggun MCP integration, you can draft, triage, summarise emails, and much more, all without leaving the terminal or the app, whichever you prefer.
Table of Contents
Connect Taggun without Auth hassles
We manage OAuth, API Key, token refresh, and scopes, you just build.
Try for FreeIntroduction
Also integrate Taggun with
Why use Composio?
Apart from a managed and hosted MCP server, you will get:
- CodeAct: A dedicated workbench that allows GPT to write its code to handle complex tool chaining. Reduces to-and-fro with LLMs for frequent tool calling.
- Large tool responses: Handle them to minimise context rot.
- Dynamic just-in-time access to 20,000 tools across 1000+ other Apps for cross-app workflows. It loads the tools you need, so GPTs aren't overwhelmed by tools you don't need.
How to install Taggun MCP in Codex
Run the setup command
Run this command in your terminal to add the Composio MCP server to Codex.
It will initiate the authentication in a browser window, authorize Codex to access your Composio account.
(Optional) Authenticate with OAuth
To authenticate manually, run the login command to open a browser window and authorize Codex to access your Composio account.
Verify the connection
Run codex mcp list to confirm Composio appears as a registered MCP server.
Codex App
Codex App follows the same approach as VS Code.
- Click ⚙️ on the bottom left → MCP Servers → + Add servers → Streamable HTTP:
- Fill the header and Key fields with
{ "x-consumer-api-key" = "ck_*******" }. - The Key is the Composio API key, that you can find on dashboard.composio.dev
- Click on Authenticate and authorize Codex to your Composio account and you're all set.
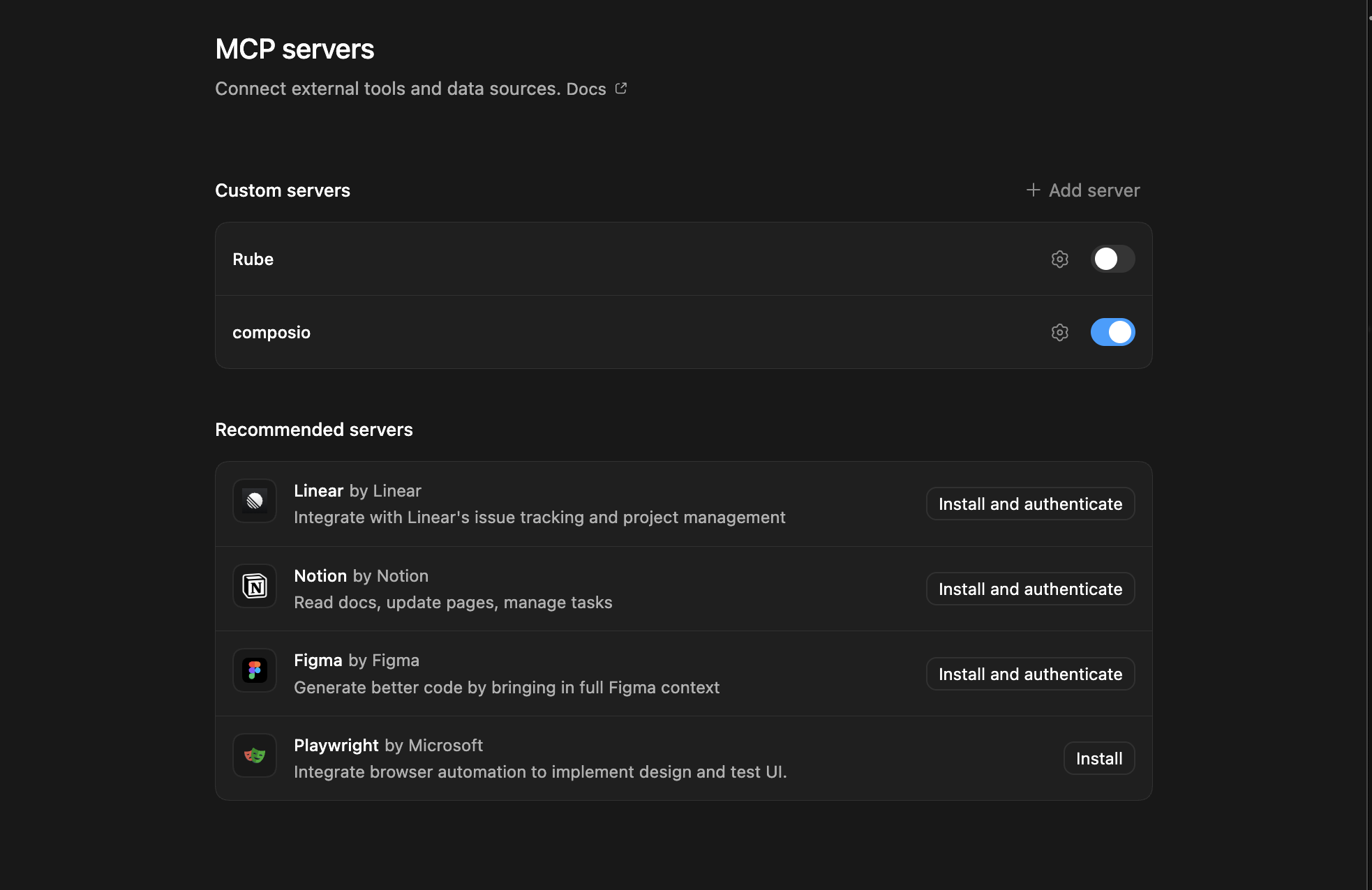
- Restart and verify if it's there in
.codex/config.toml
What is the Taggun MCP server, and what's possible with it?
The Taggun MCP server is an implementation of the Model Context Protocol that connects your AI agent and assistants like Claude, Cursor, etc directly to your Taggun account. It provides structured and secure access to real-time receipt OCR and merchant management, so your agent can scan receipts, extract detailed data, validate image URLs, and manage merchant records on your behalf.
- Instant receipt data extraction: Have your agent process receipt or invoice images via public URLs to pull out structured purchase data quickly and accurately.
- Detailed line item analysis: Use verbose extraction to get comprehensive data including line items, merchant info, and confidence metrics from receipt images or PDFs.
- Automated merchant registry management: Export the full list of known merchants for audits or synchronize merchant data directly through your agent.
- Receipt image URL validation: Let your agent check if a receipt image URL meets campaign and validation requirements before processing.
- Generate merchant mock CSVs for testing: Easily create sample merchant CSV files to test or bulk import merchant data as part of your automation workflow.
Supported Tools & Triggers
Conclusion
You've successfully integrated Taggun with Codex using Composio's MCP server. Now you can interact with Taggun directly from your terminal, VS Code, or the Codex App using natural language commands.
Key benefits of this setup:
- Seamless integration across CLI, VS Code, and standalone app
- Natural language commands for Taggun operations
- Managed authentication through Composio
- Access to 20,000+ tools across 1000+ apps for cross-app workflows
- CodeAct workbench for complex tool chaining
Next steps:
- Try asking Codex to perform various Taggun operations
- Explore cross-app workflows by connecting more toolkits
- Build automation scripts that leverage Codex's AI capabilities