Create project api keyCreates a 'publishable' or 'secret' API key for an existing Supabase project, optionally with a description; 'secret' keys can have customized JWT templates.
Delete an API key from the projectPermanently deletes a specific API key (identified by `id`) from a Supabase project (identified by `ref`), revoking its access.
Delete third party auth configRemoves a third-party authentication provider (e.
Get a third-party integrationRetrieves the detailed configuration for a specific third-party authentication (TPA) provider, identified by `tpa_id`, within an existing Supabase project specified by `ref`.
List third-party auth integrations for projectLists all configured third-party authentication provider integrations for an existing Supabase project (using its `ref`), suitable for read-only auditing or verifying current authentication settings.
Update an API key for the projectUpdates an existing Supabase project API key's `description` and/or `secret_jwt_template` (which defines its `role`); does not regenerate the key string.
Apply a database migrationTool to apply database migrations to a Supabase project.
Beta activate custom hostname for projectActivates a previously configured custom hostname for a Supabase project, assuming DNS settings are verified externally.
Activate vanity subdomain for projectActivates a vanity subdomain for the specified Supabase project (e.
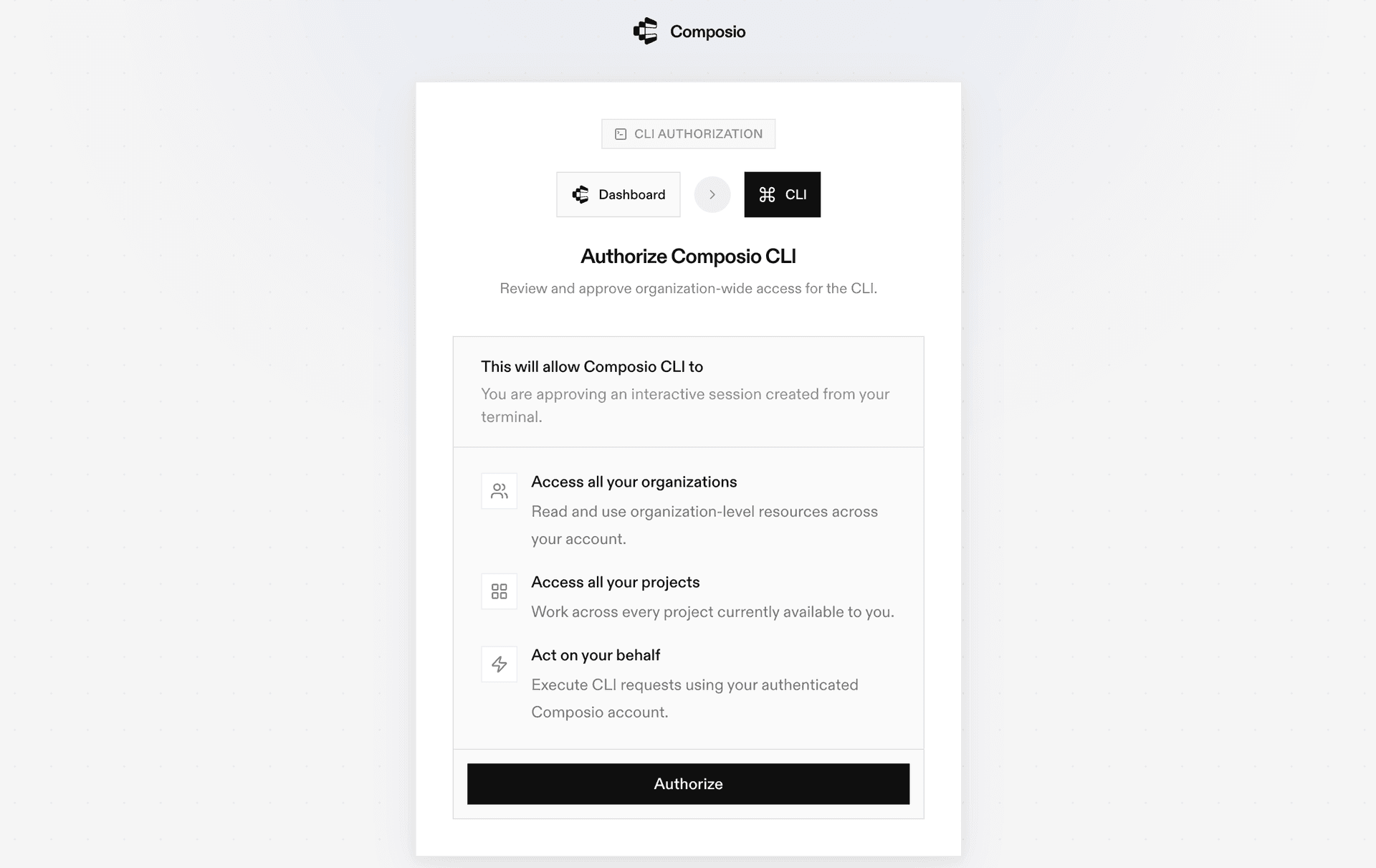
Authorize user through OAuthGenerates a Supabase OAuth 2.
Check vanity subdomain availabilityChecks if a specific vanity subdomain is available for a Supabase project; this action does not reserve or assign the subdomain.
Setup read replica for projectProvisions a read-only replica for a Supabase project in a specified, Supabase-supported AWS region to enhance read performance and reduce latency.
Enable project database webhooksEnables database webhooks for the Supabase project `ref`, triggering real-time notifications for INSERT, UPDATE, or DELETE events.
Beta get project's custom hostname configRetrieves a Supabase project's custom hostname configuration, including its status, SSL certificate, and ownership verification, noting that availability may depend on the project's plan.
Retrieve network bans for projectRetrieves the list of banned IPv4 addresses for a Supabase project using its unique project reference string; this is a read-only operation.
Get project network restrictionsRetrieves the network restriction settings (IP allowlists) for a Supabase project.
Get project pgsodium configRetrieves the PGSodium configuration, including the root encryption key, for an existing Supabase project identified by its `ref`.
Get project SSL enforcement configurationRetrieves the SSL enforcement configuration for a specified Supabase project, indicating if SSL connections are mandated for its database.
Get current vanity subdomain configFetches the current vanity subdomain configuration, including its status and custom domain name, for a Supabase project identified by its reference ID.
Remove project network bansRemoves specified IPv4 addresses from a Supabase project's network ban list, granting immediate access; IPs not currently banned are ignored.
Remove read replicaRemove a read replica from a Supabase project (Pro plan or higher required).
Execute project database queryExecutes a given SQL query against the project's database; use for advanced data operations or when standard API endpoints are insufficient, ensuring queries are valid PostgreSQL and sanitized.
Beta update project network restrictionsUpdates and applies network access restrictions (IPv4/IPv6 CIDR lists) for a Supabase project, which may terminate existing connections not matching the new rules.
Upgrade the project's PostgreSQL versionInitiates an asynchronous upgrade of a Supabase project's PostgreSQL database to a specified `target_version` from a selected `release_channel`, returning a `tracking_id` to monitor status; the `target_version` must be available in the chosen channel.
Count action runsCounts the number of action runs for a Supabase project using a HEAD request.
Create new projectCreates a new Supabase project, requiring a unique name (no dots) within the organization; project creation is asynchronous.
Bulk create secretsTool to bulk create secrets for a Supabase project.
Create a database branchCreates a new, isolated database branch from an existing Supabase project (identified by `ref`), useful for setting up separate environments like development or testing, which can optionally be linked to a Git branch.
Create a functionCreates a new serverless Edge Function for a Supabase project (identified by `ref`), requiring valid JavaScript/TypeScript in `body` and a project-unique `slug` identifier.
Create CLI login roleCreates a temporary CLI login role for database access with specified permissions; use when setting up CLI authentication for development or administrative tasks.
Create an organizationCreates a new Supabase organization, which serves as a top-level container for projects, billing, and team access.
Create project signing keyCreate a new signing key for JWT authentication in a Supabase project.
Create SSO provider configurationCreates a new SAML 2.
Create a new third-party auth integrationCall this to add a new third-party authentication method (OIDC or JWKS) to a Supabase project for integrating external identity providers (e.
Delete custom hostname configDeletes an active custom hostname configuration for the project identified by `ref`, reverting to the default Supabase-provided hostname; this action immediately makes the project inaccessible via the custom domain and requires subsequent updates to client, OAuth, and DNS settings.
Delete branch by idPermanently and irreversibly deletes a specific, non-default database branch by its `branch_id`, without affecting other branches.
Delete an edge function by slugPermanently deletes a specific Edge Function (by `function_slug`) from a Supabase project (by `ref`); this action is irreversible and requires prior existence of both project and function.
Delete CLI login roles[Beta] Deletes existing login roles used by the Supabase CLI for the specified project.
Delete project by refPermanently and irreversibly deletes a Supabase project, identified by its unique `ref` ID, resulting in complete data loss.
Delete vanity subdomain for projectPermanently and irreversibly deletes an active vanity subdomain configuration for the specified Supabase project, reverting it to its default Supabase URL.
Bulk delete secretsTool to bulk delete secrets from a Supabase project.
Remove an SSO providerDeletes a specific SSO provider by its ID (`provider_id`) from a Supabase project (`ref`), which disables it and returns its details; ensure this action will not inadvertently lock out users.
Deploy functionDeploys Edge Functions to a Supabase project using multipart upload.
Disable preview branchingDisables the preview branching feature for an existing Supabase project, identified by its unique reference ID (`ref`).
Disable project readonly modeTemporarily disables a Supabase project's read-only mode for 15 minutes to allow write operations (e.
Exchange auth code for access and refresh token(Beta) Implements the OAuth 2.
Generate TypeScript typesGenerates and retrieves TypeScript types from a Supabase project's database; any schemas specified in `included_schemas` must exist in the project.
Get action run statusRetrieves the status and details of a specific action run, including its steps, timestamps, and configuration.
Get action run logsRetrieves the execution logs for a specific action run by its ID.
Get Available RegionsTool to get the list of available regions for creating a new Supabase project.
Get a database branchRetrieves detailed information about a specific database branch by its name and project reference.
Get database branch configRetrieves the read-only configuration and status for a Supabase database branch, typically for monitoring or verifying its settings.
Retrieve a functionRetrieves detailed information, metadata, configuration, and status for a specific Edge Function using its project reference ID and function slug.
Retrieve a function bodyRetrieves the source code (body) for a specified serverless Edge Function using its project reference and function slug; this is a read-only operation that does not execute the function or return runtime logs.
Get API Health StatusTool to check the health status of the Supabase API.
Get JIT access config[Beta] Retrieves the project's just-in-time (JIT) access configuration, including user roles and their expiration settings.
Get a migrationRetrieves a specific database migration entry from the migration history using its version identifier.
Get information about an organizationFetches comprehensive details for a specific Supabase organization using its unique slug.
Get projectRetrieves detailed information about a specific Supabase project by its unique reference ID.
Get project API keyRetrieves details of a specific API key for a Supabase project by its UUID.
Get project API keysRetrieves all API keys for an existing Supabase project, specified by its unique reference ID (`ref`); this is a read-only operation.
Get project logsRetrieves analytics logs for a Supabase project.
Get project PgBouncer configRetrieves the active PgBouncer configuration (PostgreSQL connection pooler) for a Supabase project, used for performance tuning, auditing, or getting the connection string.
Get project postgres configRetrieves the current read-only PostgreSQL database configuration for a specified Supabase project's `ref`, noting that some advanced or security-sensitive details might be omitted from the response.
Get project's PostgREST configRetrieves the PostgREST configuration for a specific Supabase project.
Get project's read-only mode statusRetrieves the read-only mode status for a specified Supabase project to check its operational state; this action does not change the read-only state.
Get project signing keysTool to list all signing keys for a Supabase project.
Get project Supavisor configurationRetrieves the Supavisor (connection pooler) configuration for a specified Supabase project, identified by its reference ID.
Get Project Upgrade EligibilityChecks a Supabase project's eligibility for an upgrade, verifying compatibility and identifying potential issues; this action does not perform the actual upgrade.
Get project upgrade statusRetrieves the latest status of a Supabase project's database upgrade for monitoring purposes; does not initiate or modify upgrades.
Get TUS resumable upload base optionsHandles OPTIONS request for TUS Resumable uploads to discover server capabilities.
Get TUS resumable upload optionsHandles OPTIONS request for TUS Resumable uploads to discover server capabilities.
Get project's auth configRetrieves the project's complete read-only authentication configuration, detailing all settings (e.
Get project's service health statusRetrieves the current health status for a Supabase project, for specified services or all services if the 'services' list is omitted.
Get a specific SQL snippetRetrieves a specific SQL snippet by its unique identifier.
Get a SSO provider by its UUIDRetrieves the configuration details for a specific Single Sign-On (SSO) provider (e.
Get Table SchemasRetrieves column details, types, and constraints for multiple database tables to help debug schema issues and write accurate SQL queries.
OPTIONS for resumable upload signHandles CORS preflight OPTIONS request for TUS resumable upload signing.
OPTIONS for resumable upload signHandles CORS preflight OPTIONS request for TUS resumable upload signing endpoints.
Invoke Edge FunctionTool to invoke a deployed Supabase Edge Function over HTTPS.
List all organizationsLists all organizations (ID and name only) associated with the Supabase account, excluding project details within these organizations.
List all projectsRetrieves a list of all Supabase projects, including their ID, name, region, and status, for the authenticated user.
List project database backupsLists all database backups for a Supabase project, providing details on existing backups but not creating new ones or performing restores; availability may depend on plan and configuration.
List all bucketsRetrieves a list of all storage buckets for a Supabase project, without returning bucket contents or access policies.
List all database branchesLists all database branches for a specified Supabase project, used for isolated development and testing of schema changes; ensure the project reference ID is valid.
List all functionsLists metadata for all Edge Functions in a Supabase project (specified by 'ref'), excluding function code or logs; the project must exist.
List migration historyRetrieves the list of applied database migration versions for a Supabase project.
List members of an organizationRetrieves all members of a Supabase organization, identified by its unique slug, including their user ID, username, email, role, and MFA status.
List all secretsRetrieves all secrets for a Supabase project using its reference ID; secret values in the response may be masked.
List SQL snippets for the logged in userRetrieves a list of SQL snippets for the logged-in user, optionally filtered by a specific Supabase project if `project_ref` is provided.
List all SSO providersLists all configured Single Sign-On (SSO) providers for a Supabase project, requiring the project reference ID (`ref`) of an existing project.
List Database TablesLists all tables and views in specified database schemas, providing a quick overview of database structure to help identify available tables before fetching detailed schemas.
Patch a migration[Beta] Patches an existing entry in the project's migration history, updating the name or rollback script.
Patch project network restrictionsUpdates project's network restrictions by incrementally adding or removing IPv4/IPv6 CIDR blocks.
Push a database branchPushes a database branch, applying migrations and changes to the specified branch.
Reset a database branchResets an existing Supabase database branch, identified by `branch_id`, to its initial clean state, irreversibly deleting all its current data and schema changes.
Restore database PITR backupRestores a Supabase project's database to a specific Unix timestamp using Point-in-Time Recovery (PITR), overwriting the current state; requires a paid plan with PITR and physical backups enabled.
Execute read-only database query[Beta] Run a SQL query as supabase_read_only_user.
Select From TableTool to select rows from a Supabase/PostgREST table.
Update a functionUpdates an existing Supabase Edge Function's properties (like name, slug, source code, JWT settings, import map) identified by project `ref` and `function_slug`, supporting plain text code or ESZIP for the body.
Update database branch configUpdates the configuration of a Supabase database branch, allowing modification of its name, associated Git branch, reset-on-push behavior, persistence, and status.
Update database passwordUpdates the database password for a Supabase project.
Bulk update functionsTool to bulk update Edge Functions in a Supabase project.
Update JIT access config[Beta] Update a Supabase project's just-in-time (JIT) access configuration.
Update pgsodium root keyCritically updates or initializes a Supabase project's pgsodium root encryption key for security setup or key rotation, requiring secure backup of the new key to prevent irreversible data loss.
Update a projectUpdates a Supabase project's configuration (currently supports updating the project name).
Update project's auth configUpdate Supabase project Auth configuration via the Management API.
Update project's custom hostname configurationUpdates the custom hostname for a Supabase project, requiring subsequent DNS changes to a user-controlled domain for SSL certificate issuance and domain ownership.
Update project legacy API keysTool to disable or re-enable JWT-based legacy API keys (anon, service_role) for a Supabase project.
Update project's postgres configUpdates specified PostgreSQL configuration parameters for an existing Supabase project (`ref`) to optimize database performance; note that unspecified parameters remain unchanged, and caution is advised as incorrect settings can impact stability or require a restart.
Update project's PostgREST configUpdates PostgREST configuration settings (e.
Update database pooler configUpdates the Supavisor (database pooler) configuration, such as `default_pool_size`, for an existing Supabase project identified by `ref`; the `pool_mode` parameter in the request is deprecated and ignored.
Update SSL enforcement configUpdates the SSL enforcement configuration (enable/disable) for a specified Supabase project's database.
Update an SSO provider by its UUIDUpdates an existing SSO provider's SAML metadata, associated email domains, or attribute mappings for a Supabase project, identified by `ref` and `provider_id`.
Upsert migrationTool to upsert a database migration without applying it.
Reverify custom hostnameRe-verifies DNS and SSL configurations for an existing custom hostname associated with a Supabase project.