Cowork is Anthropic's AI agent for knowledge work. Think of it as Claude Code for everything else. It works autonomously with your computer, local files, and applications to accomplish complex tasks.
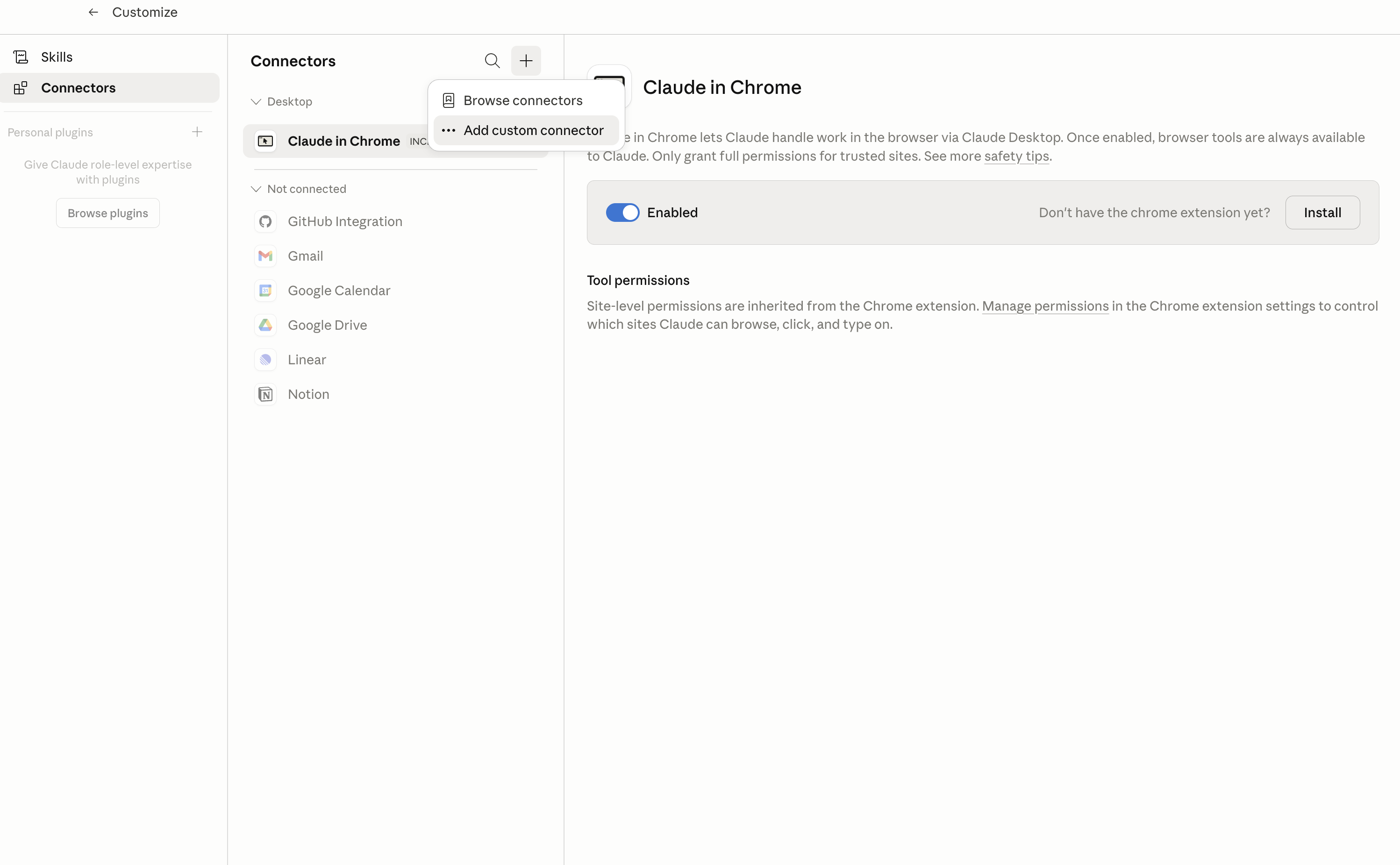
This guide walks you through the easiest and most secure way to connect your Dock certs account to Cowork via Composio Connect, enabling it to list all credentials issued this month, delete a credential by its ID, create a webhook for credential updates, and more such actions on your behalf without compromising your account security.